Torzon Access — How to Access the Marketplace Safely
Access Torzon Market through the Tor network with verified onion links, PGP authentication, and proper security configuration. This guide covers everything you need to connect to the Torzon marketplace in 2026, from downloading Tor Browser to setting up encrypted communications and cryptocurrency wallets.
torzonz4wmukuvm6nh4rtgkk76t3lcubr7rm3yvqjqvvvomaw3hmjuid.onion
Open in Tor Browser — View all Torzon mirrors →
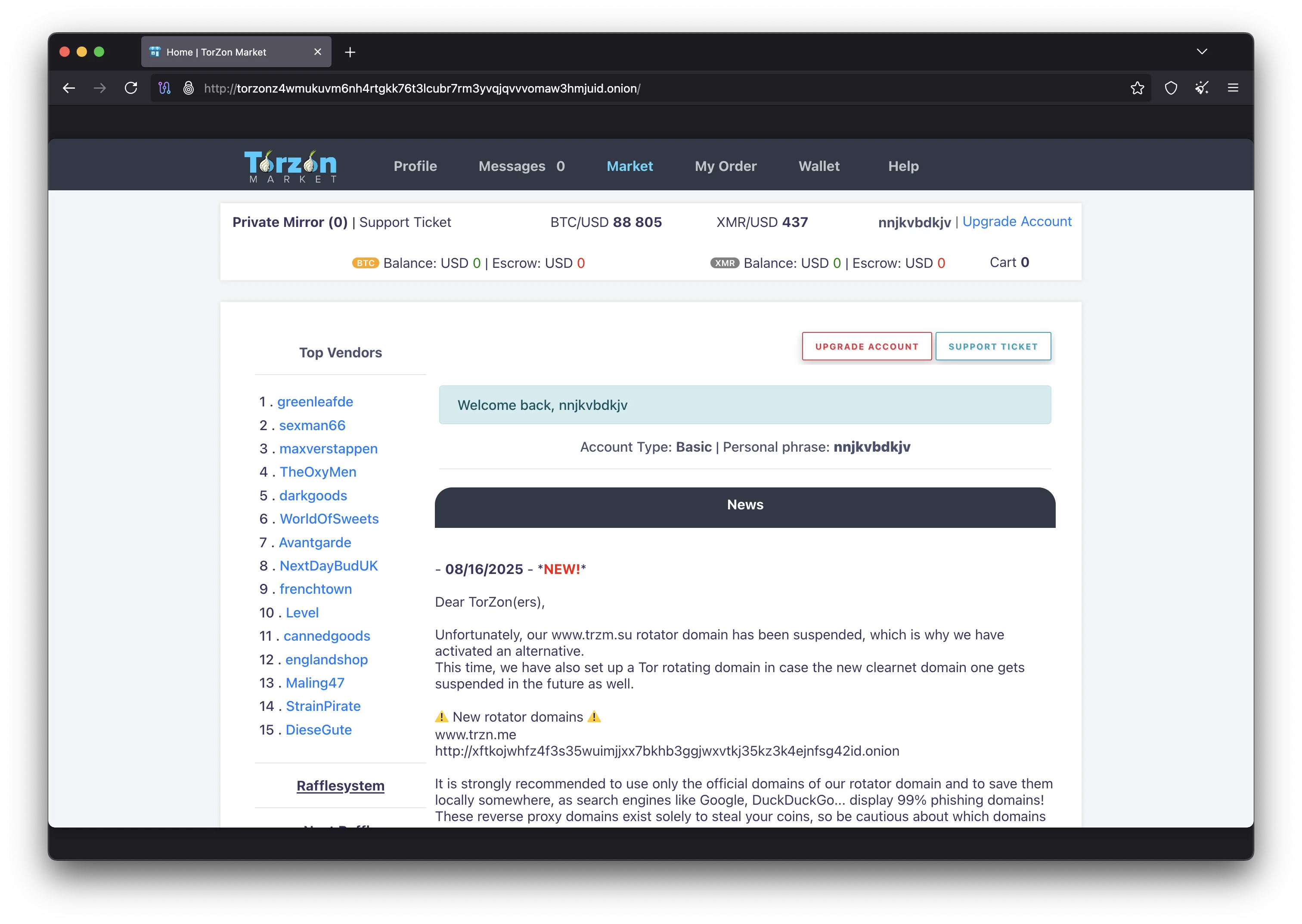
Torzon Market is one of the most active darknet marketplaces operating in 2026, with over 20,000 listings from more than 2,000 vendors. The platform launched in September 2022 and has maintained consistent uptime above 98% while processing an estimated $15 million in annual turnover. Torzon operates as a hidden service on the Tor network, meaning it can only be accessed through Tor Browser using its official .onion address. This guide walks you through every step required to access Torzon safely, from installing the right software to verifying your connection and protecting your privacy throughout the process.
The marketplace has earned its position as one of the most trusted platforms because of its focus on advanced security technology. It was the first darknet market to implement post-quantum cryptography, protecting user data against future quantum computing attacks. The platform supports multiple authentication methods including PGP two-factor authentication, TOTP authenticator apps, and FIDO2/WebAuthn hardware security keys. Every transaction goes through a 2-of-3 multisig escrow system that prevents any single party from controlling funds. These features, combined with a multi-layer anti-phishing system and zero-knowledge RAM-only servers, make Torzon one of the most secure marketplaces available today.
Before you begin, it is important to understand that accessing any hidden service requires specific tools and knowledge. You cannot visit a .onion address with a regular browser like Chrome or Firefox. The Tor network encrypts your traffic and routes it through multiple relays around the world, making it nearly impossible to trace your connection back to your physical location. This anonymity layer is what makes the encrypted marketplace accessible to buyers and sellers who value their privacy. Read on for a complete breakdown of how to access the marketplace safely, or visit the main Torzon site for a general overview. Our detailed access guide covers each step in depth and what security measures you should put in place before your first visit.
How to Access Torzon Market in 6 Steps
Accessing the marketplace requires following a specific sequence of steps to ensure your connection is both anonymous and authenticated. Each step builds on the previous one, creating multiple layers of protection between your real identity and your marketplace activity. The following six-step process is the recommended approach for first-time users who want to access the platform without making common security mistakes. Experienced users who already have Tor Browser installed and a PGP key configured can skip directly to the link verification step.
Download Tor Browser
The first step to accessing Torzon is downloading Tor Browser from the official Tor Project website. Tor Browser is a modified version of Firefox that automatically routes all your web traffic through the Tor network. This prevents your internet service provider, network administrators, and surveillance systems from seeing which websites you visit. Download only from torproject.org to avoid tampered copies. After downloading, verify the file signature using the signing key published on the Tor Project website to confirm the installer has not been modified. Tor Browser is available for Windows, macOS, Linux, and Android. Install it like any other application and run it without administrator privileges for better security isolation.
Configure Security Settings
After installing Tor Browser, open the application and click Connect. Once connected to the Tor network, navigate to the security settings by clicking the shield icon in the toolbar. Set the security level to Safest, which disables JavaScript, certain fonts, and media features that could be used to identify your browser or exploit vulnerabilities. This setting provides the maximum protection available in Tor Browser. The marketplace is designed to work with JavaScript disabled, so you will not lose any functionality by using the Safest setting. Also consider disabling WebRTC in the advanced settings, though Tor Browser blocks WebRTC leaks by default. Check the Electronic Frontier Foundation resources for additional browser security tips.
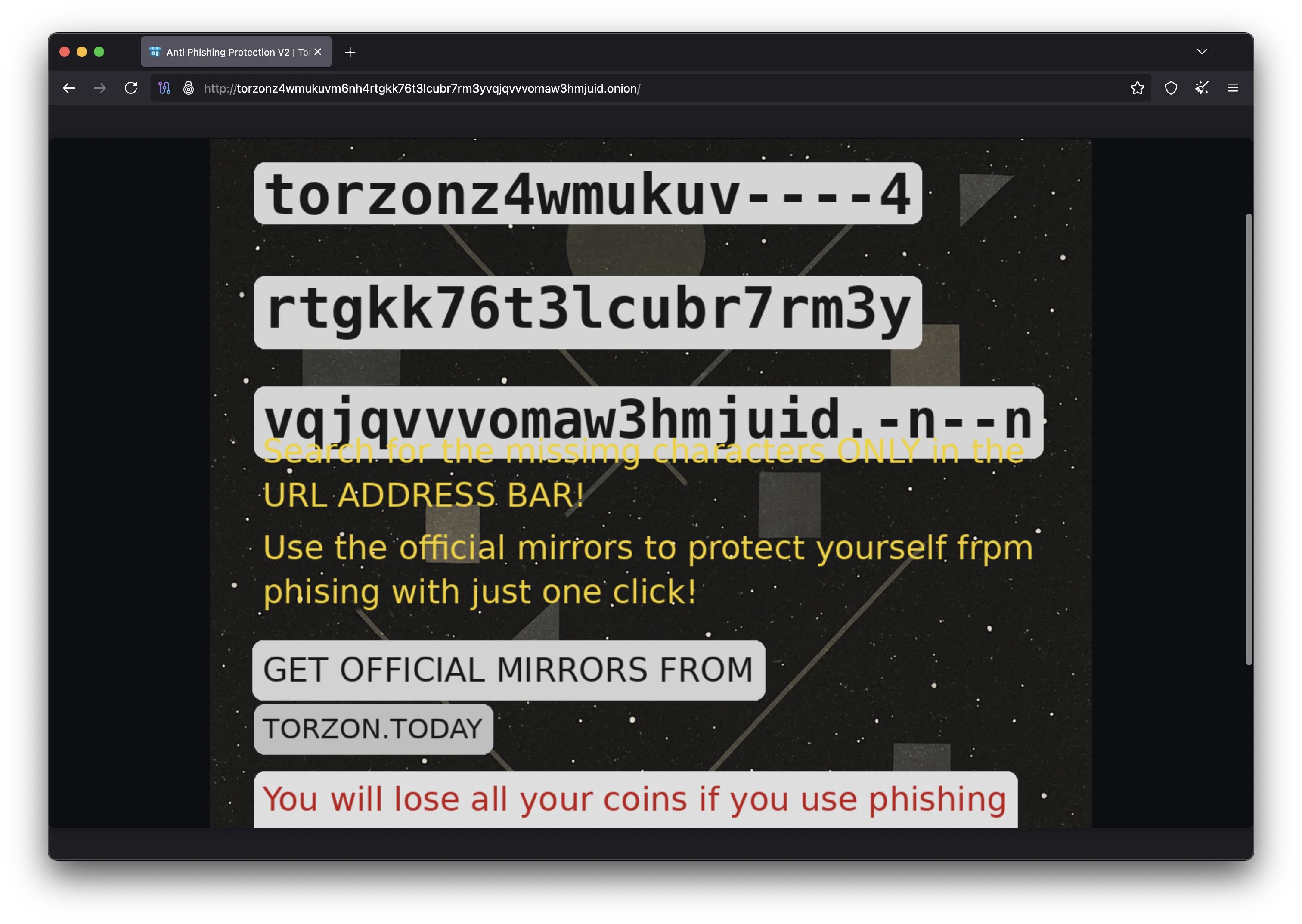
Get Verified Torzon Links
Never search for Torzon links on regular search engines or click links shared in random Telegram groups. Phishing sites that impersonate the Torzon marketplace are common and designed to steal your credentials and funds. The safest way to get a verified Torzon .onion address is through official channels: this page (access.torzondnm.world), the Torzon links page, or the official Torzon page. Each of these sources publishes the same PGP-signed mirror list that you can verify independently. The primary Torzon onion address is: torzonz4wmukuvm6nh4rtgkk76t3lcubr7rm3yvqjqvvvomaw3hmjuid.onion
Verify Links with PGP
Before pasting any onion URL into Tor Browser, verify it with the official Torzon PGP key. Install GnuPG on your system and import the Torzon Market public key. Check that the key fingerprint matches what is published across multiple official sources. Then download the signed mirror list file and run gpg --verify to confirm the signature is valid. If the verification output says "Good signature from Torzon Market," the links in the file are authentic. If verification fails, do not use those links under any circumstances. PGP verification is the only reliable way to distinguish genuine Torzon addresses from phishing sites, since phishing domains can look identical to the real marketplace. Learn more about PGP at OpenPGP.org.
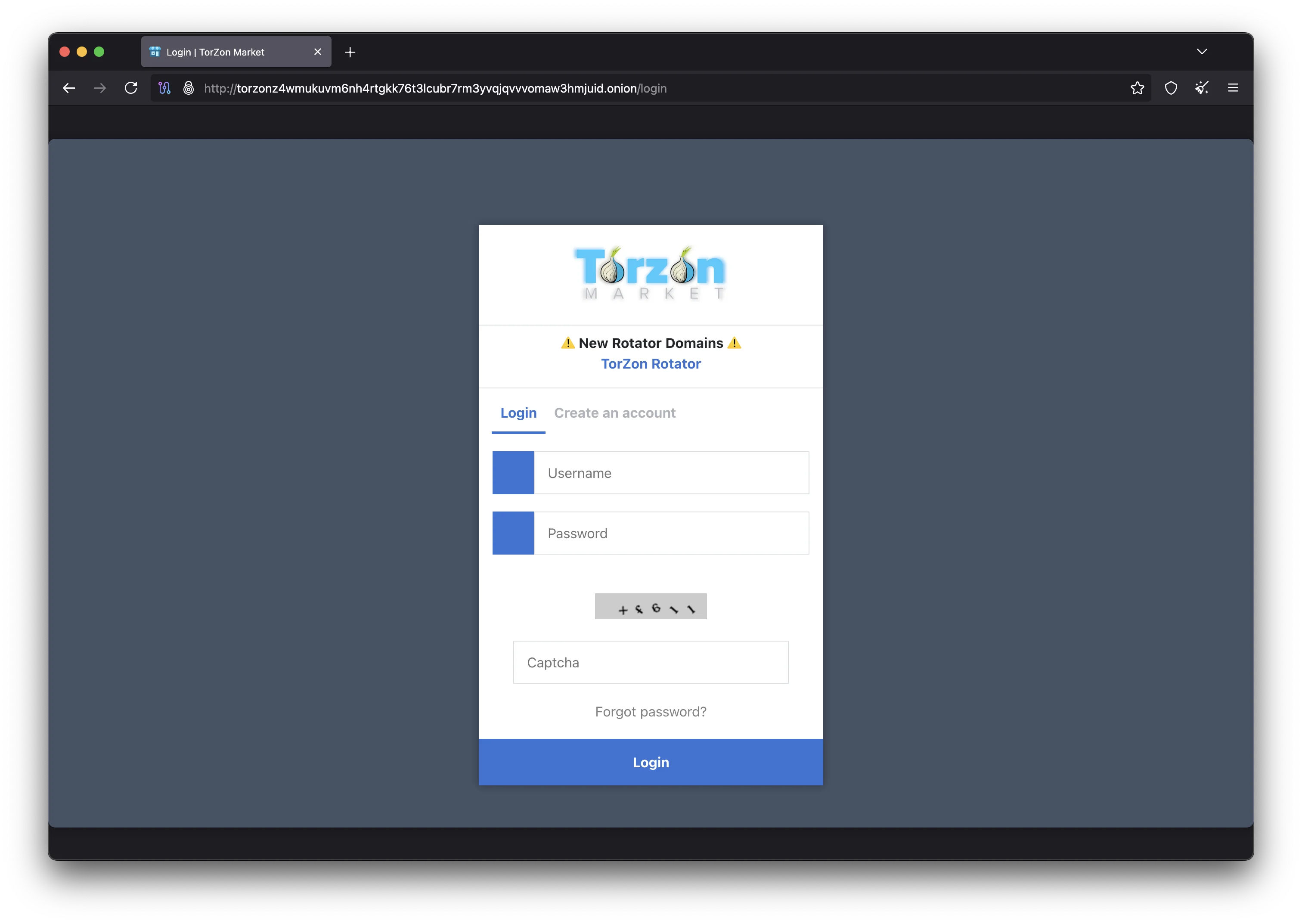
Access the Torzon Marketplace
With a verified .onion address in hand, paste it into the Tor Browser address bar and press Enter. The Tor network will route your connection through three encrypted relays before reaching the Torzon hidden service. This process takes a few seconds longer than regular browsing because of the encryption overhead. Once the login page loads, verify that your anti-phishing indicators are correct before entering any credentials. If you are a returning user, check that your personal security phrase, security image, and color scheme match what you configured during registration. If any element is wrong or missing, you may be on a phishing site and should close the tab immediately. New users will see the standard Torzon registration page without personalized anti-phishing elements.
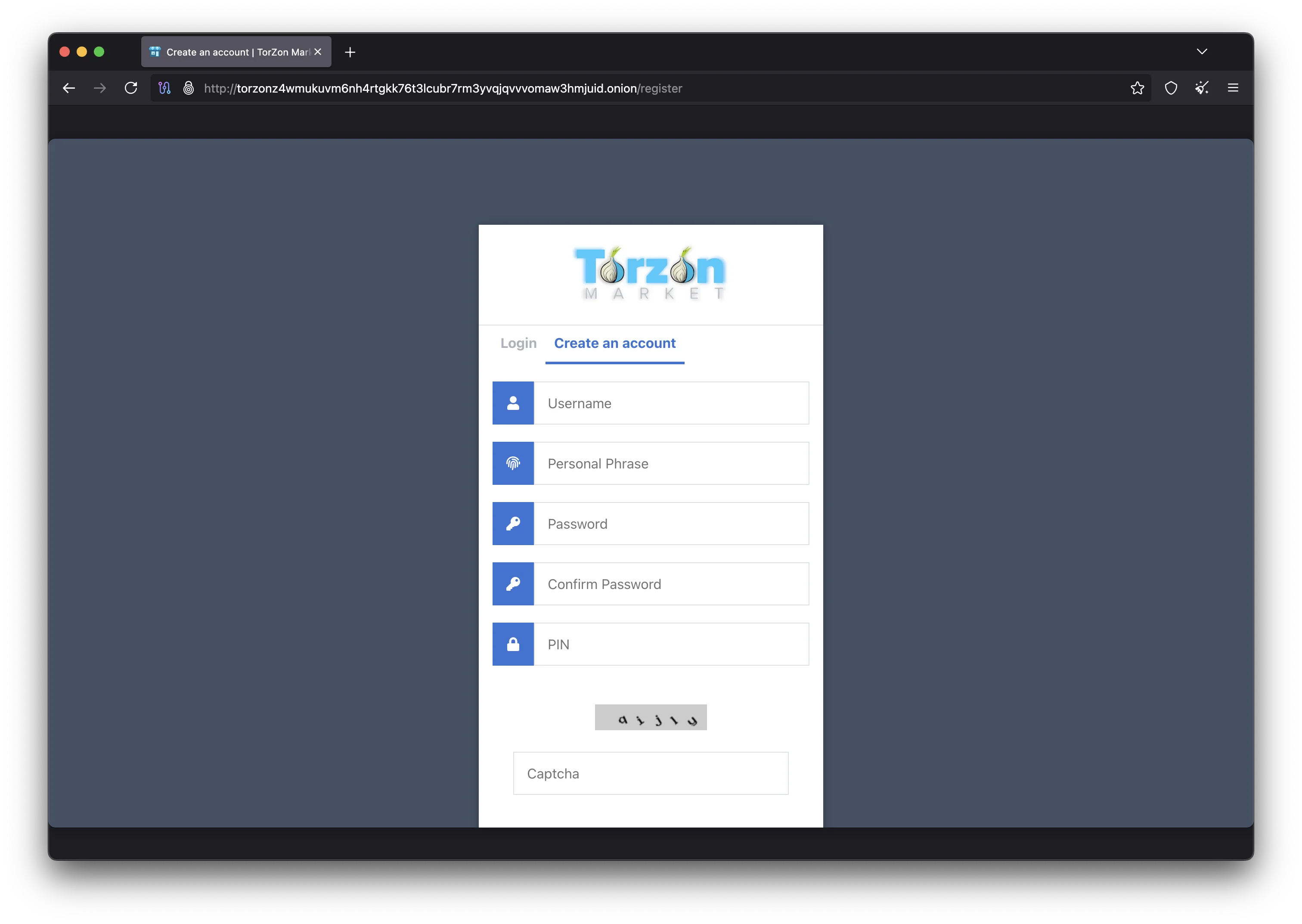
Set Up Your Account with PGP 2FA
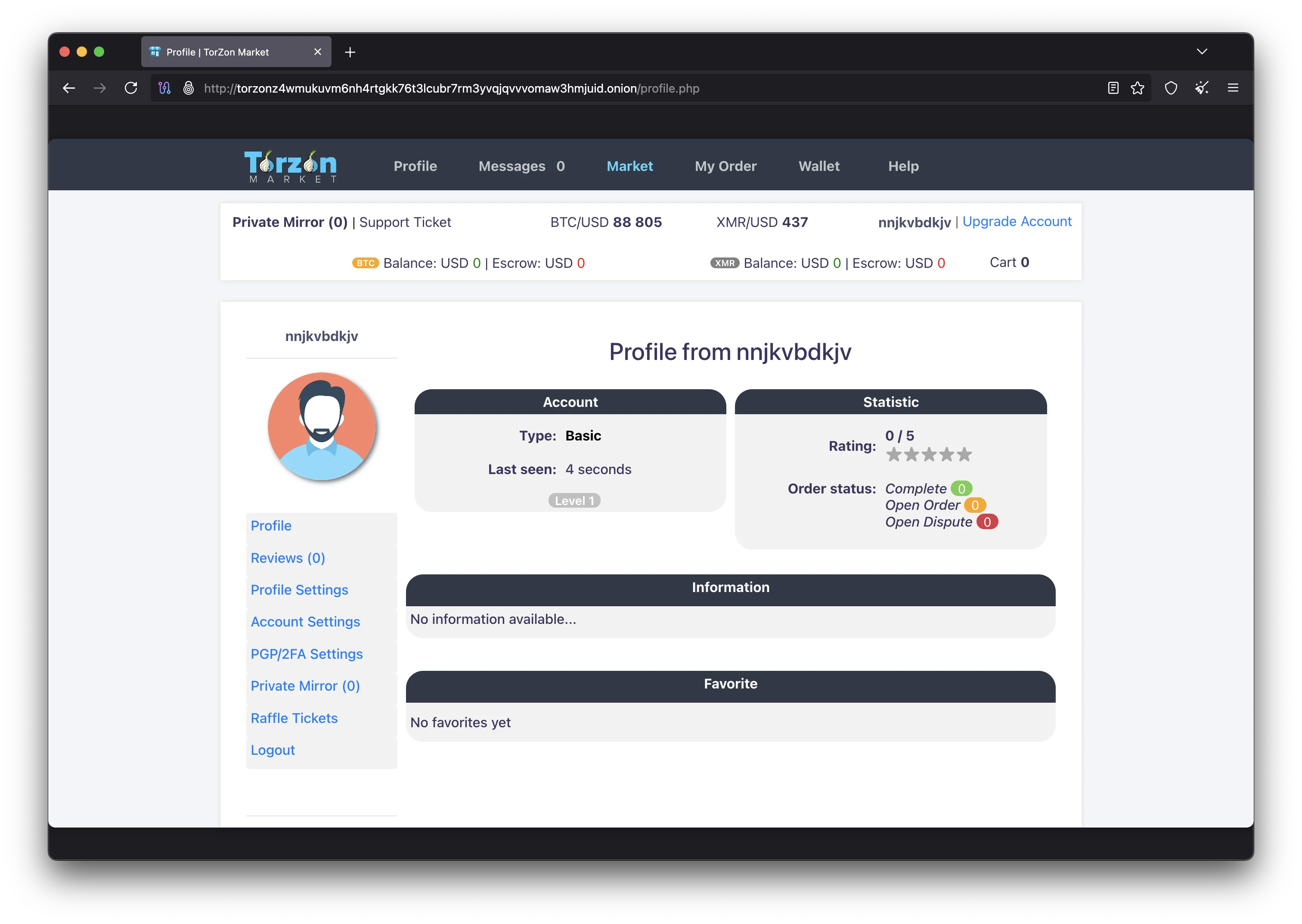
During registration on the platform, you will be asked to provide a username and a PGP public key. Generate a 4096-bit RSA key pair using GnuPG if you do not already have one. Paste your public key into the registration form. This enables PGP two-factor authentication, which means every login attempt will require you to decrypt a challenge message that is encrypted with your public key. Only someone with the corresponding private key can decrypt it, making account takeover virtually impossible. After registration, configure your anti-phishing settings: choose a personal security phrase that only you would recognize, select a security image, and pick a color scheme. These three elements will appear on every legitimate login page, letting you verify the site is genuine before you type anything. The platform also supports TOTP authenticator apps and FIDO2/WebAuthn hardware security keys as additional authentication options.
Why the Tor Network Protects Your Privacy
The Tor network is the foundation that makes anonymous access to the Torzon marketplace possible. Understanding how Tor works helps you appreciate why certain security practices matter and what risks remain even with Tor Browser installed. Tor was originally developed by the United States Naval Research Laboratory and is now maintained by the Tor Project, a nonprofit organization supported by the Electronic Frontier Foundation and other privacy advocates around the world.
When you connect to a hidden service like Torzon through Tor Browser, your traffic is encrypted in three layers and routed through three separate relay nodes. The entry guard relay knows your IP address but cannot see your destination. The middle relay only knows the addresses of the relays on either side of it. The exit relay (or in the case of hidden services, the rendezvous point) connects to the destination but does not know who you are. This architecture means no single node in the circuit can connect your identity to the site you are visiting. Even if an attacker controls one relay, they cannot determine both the source and destination of the traffic.
Hidden services like the Torzon marketplace add another privacy layer on top of this architecture. Unlike regular websites that use exit relays to reach the public internet, hidden services keep all traffic within the Tor network. The Torzon .onion address is derived from the marketplace's cryptographic key, so the address itself proves the identity of the server. No DNS lookups, no IP address exposure, and no plaintext traffic leaves the Tor network at any point. This is why accessing Torzon through its .onion address is fundamentally more private than visiting a regular website, even with a VPN. For a deeper understanding of onion routing, consult the Wikipedia article on Tor.
Tor hidden services also provide forward secrecy for all connections. Each session establishes a new set of encryption keys, so even if a key is compromised in the future, previously recorded traffic cannot be decrypted. The Torzon marketplace takes this further with its post-quantum cryptography implementation, which uses algorithms that are resistant to attacks from both classical and quantum computers. This means that encrypted data captured today will remain protected even if quantum computers become powerful enough to break current encryption standards in the coming decades.
Torzon Market Security Features
The marketplace has built one of the most advanced security architectures found on any darknet platform. Each feature addresses a specific threat vector, from phishing attacks and account compromise to fund theft and server seizure. Understanding these security features helps you take full advantage of the protections the platform provides and identify potential risks that require additional precautions on your side.
2-of-3 Multisig Escrow
Every transaction on the marketplace goes through a 2-of-3 multisig escrow system. Three cryptographic keys are generated for each transaction: one held by the buyer, one by the vendor, and one by the marketplace. Funds can only be released when two of the three parties sign the transaction. In a normal purchase, the buyer and vendor sign to release payment after the order is confirmed. If a dispute arises, the Torzon marketplace acts as an arbiter, reviewing evidence from both sides and signing with the winning party to release or refund the funds. This system prevents the marketplace from unilaterally accessing any funds, protecting users from the exit scam risk that has affected other platforms. The multisig escrow works with both Bitcoin and Monero, though the implementation differs slightly for each cryptocurrency due to their different transaction models.
Post-Quantum Cryptography
The platform is the first darknet marketplace to implement post-quantum cryptographic algorithms. Traditional encryption methods like RSA and ECDSA are theoretically vulnerable to quantum computing attacks. While practical quantum computers capable of breaking current encryption do not exist yet, data encrypted today could be stored by adversaries and decrypted in the future when quantum technology matures. The post-quantum implementation uses lattice-based cryptography algorithms that are resistant to both classical and quantum attacks. This protects user data, communications, and transaction details not only from current threats but also from future technological advances. The National Institute of Standards and Technology (NIST) has been standardizing post-quantum algorithms, and the marketplace's implementation aligns with these emerging standards.
PGP Authentication & 2FA
The platform supports three authentication methods to protect user accounts. The primary method is PGP two-factor authentication, where the marketplace encrypts a random challenge token with your public key during login. You must decrypt this token with your private key and submit the plaintext to prove your identity. This eliminates the risk of password theft, keyloggers, and brute-force attacks entirely. For users who prefer a simpler approach, Torzon also supports TOTP authenticator apps that generate time-based one-time codes, similar to Google Authenticator. The most advanced option is FIDO2/WebAuthn hardware security keys, which provide phishing-resistant authentication through physical USB or NFC devices. All three methods can be combined for maximum account protection on the platform.
Anti-Phishing Protection
Phishing is the number one threat to darknet marketplace users, and the platform has built a multi-layer defense system against it. During account setup, every user configures three personalized anti-phishing elements: a secret phrase that only the genuine Torzon server can display, a security image chosen from a library of unique graphics, and a custom color scheme applied to the login page. Every time you visit the real marketplace, all three elements appear exactly as you configured them. A phishing site cannot replicate these elements because they are stored encrypted on the server and tied to your account and browser session. If your personal phrase is missing, the image is wrong, or the colors do not match, you are on a fake site and should close your browser immediately. This system provides visual verification that is quick and reliable, working even on the Safest Tor Browser security setting.
Warrant Canary
The marketplace publishes a regularly updated warrant canary that cryptographically proves the marketplace has not received any secret court orders, national security letters, or gag orders from law enforcement. The canary is a PGP-signed statement that includes the current date and references to recent news events, proving it was created recently and not pre-generated. If the canary stops being updated or its PGP signature fails to verify, users should assume the marketplace may have been compromised. This transparency mechanism gives users an early warning system that is legally protected under most jurisdictions, since the marketplace is not actively disclosing the existence of an order but rather stopping a voluntary publication.
Zero-Knowledge RAM-Only Servers
The marketplace runs its infrastructure on RAM-only servers with no persistent storage. All data is kept in volatile memory that is erased immediately when the server loses power. This means that if a server is physically seized by law enforcement, all user data, encryption keys, and session information are destroyed the moment the power cable is disconnected. No hard drives, no SSDs, no data recovery possible. The marketplace synchronizes encrypted backups across multiple geographic locations, so the service can be restored quickly after any disruption, but the actual operating servers never write sensitive data to disk. This zero-knowledge architecture ensures that even the server hosting provider cannot access marketplace data.
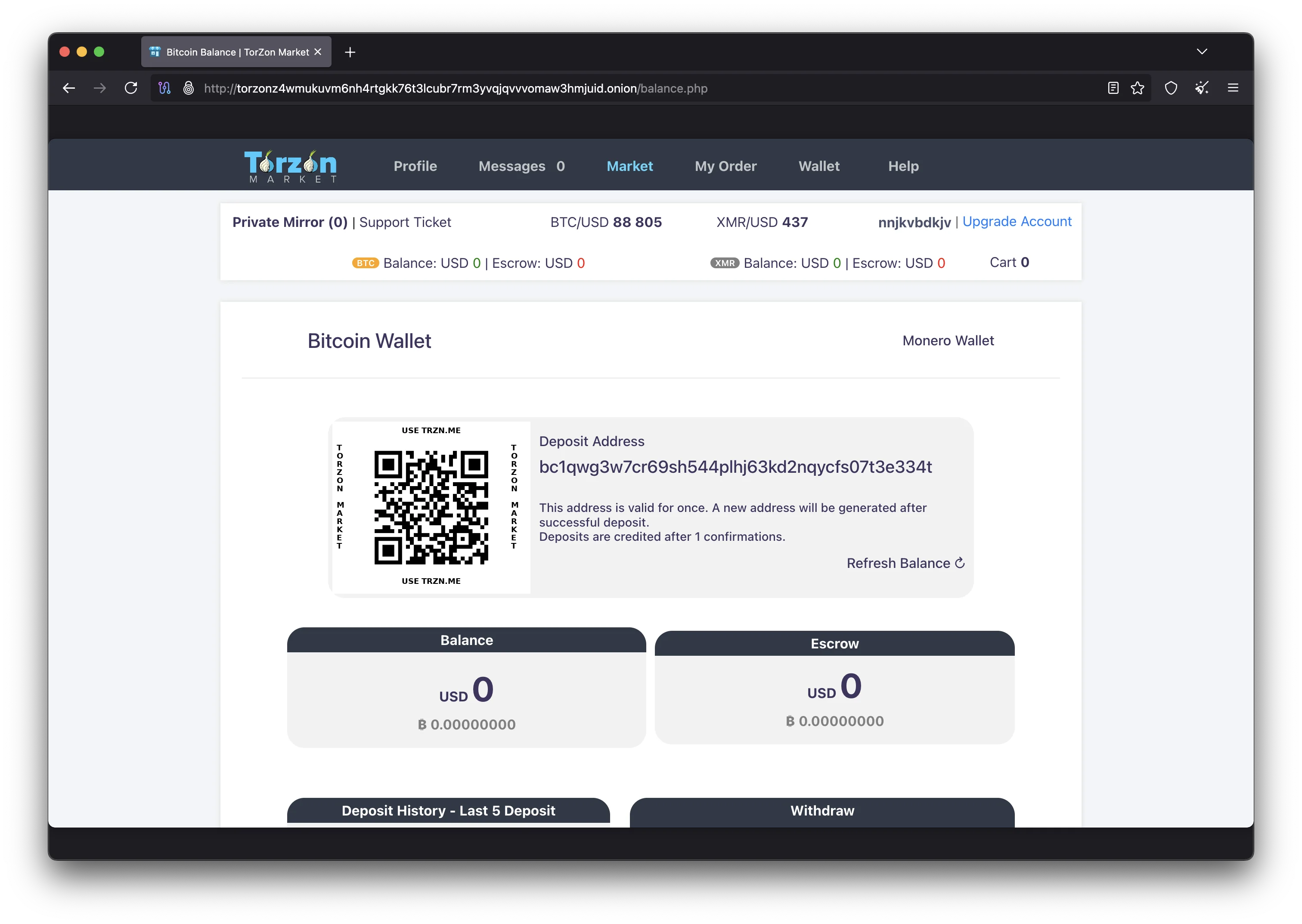
Cryptocurrency and Payments on Torzon
The marketplace accepts two cryptocurrencies: Bitcoin (BTC) and Monero (XMR). While both are supported, the platform strongly recommends Monero for all transactions due to its superior privacy properties. Understanding the differences between these two payment options and how to set up your wallets correctly is important before you start using the marketplace.
Bitcoin is the most widely known cryptocurrency, but it operates on a transparent public blockchain where every transaction is permanently recorded. Chain analysis firms can trace Bitcoin transactions across multiple hops, potentially linking marketplace activity to real-world identities if the coins were ever associated with a known exchange account. Services called Bitcoin mixers or CoinJoin implementations attempt to break this chain of traceability, but their effectiveness varies and some have been shut down by law enforcement. If you choose to use Bitcoin on the platform, consider using a dedicated wallet that has never been connected to your identity, and send coins through multiple intermediate wallets before depositing to Torzon. Visit bitcoin.org for basic Bitcoin wallet information.
Monero (XMR) is the recommended payment method on Torzon because it provides true financial privacy by default. Every Monero transaction uses three privacy technologies working together: ring signatures hide the sender among a group of possible signers, stealth addresses generate a one-time destination for each transaction so the receiver's public address never appears on the blockchain, and RingCT (Ring Confidential Transactions) hide the transaction amount. These features mean that no observer can determine who sent Monero, who received it, or how much was transferred. Chain analysis firms cannot trace Monero transactions the way they can trace Bitcoin. For the strongest privacy, download the official Monero wallet from getmonero.org and run your own local node through Tor.
To deposit funds into your marketplace wallet, navigate to the wallet section of the marketplace after logging in. You will see a unique deposit address for both BTC and XMR. Copy the address carefully and send your cryptocurrency from your personal wallet. The platform uses a confirmations system before funds appear in your marketplace balance: Bitcoin deposits typically require two to three confirmations (approximately 20 to 30 minutes), while Monero deposits require ten confirmations (approximately 20 minutes). Never send cryptocurrency from an exchange account directly to a marketplace deposit address, as exchanges may flag and freeze your account for interacting with known marketplace addresses.
Privacy Tools for Secure Torzon Access
While Tor Browser provides the baseline anonymity needed to access the Torzon marketplace, additional privacy tools can significantly strengthen your security posture. The level of protection you need depends on your personal threat model, but implementing even one or two of these tools will reduce your exposure to common attack vectors. Each tool addresses a different aspect of operational security, from protecting your operating system against malware to managing sensitive credentials and encrypting local files.
Tails OS is a portable operating system that you boot from a USB drive. It routes all internet traffic through the Tor network and leaves no trace on the computer after shutdown. Tails is based on Debian Linux and comes with Tor Browser, GnuPG, a Monero wallet, and other privacy tools pre-installed. Because Tails runs entirely in RAM and does not use the computer's hard drive, even sophisticated forensic analysis cannot recover your browsing history or downloaded files after you remove the USB and shut down. Tails is the recommended operating system for accessing the hidden service marketplace if you are using a shared or public computer, or if you want to keep your marketplace activity completely isolated from your daily computing environment.
Whonix takes a different approach by using virtual machines to isolate your network traffic. It consists of two VMs: a gateway that handles all Tor routing, and a workstation where you run your applications. Even if malware compromises the workstation VM, it cannot bypass the Tor gateway or discover your real IP address. When combined with Qubes OS, Whonix provides hardware-level isolation through Xen virtualization, creating the strongest available desktop security configuration. This setup is recommended for users who need persistent access to the marketplace and want to keep files, PGP keys, and wallet data between sessions while maintaining strong isolation. Review the Privacy Guides recommendations for choosing between Tails and Whonix based on your needs.
Password and credential management is another area where many users make critical mistakes. Use KeePassXC to generate and store strong, unique passwords for each marketplace account and cryptocurrency wallet. KeePassXC stores your credentials in an encrypted database file that you can keep on your Tails persistent volume or within your Whonix workstation. Never reuse passwords across different services, and never store marketplace credentials in a browser password manager or cloud-based password service. For encrypting sensitive files on your local machine, VeraCrypt creates encrypted volumes that appear as regular files until mounted with the correct passphrase. You can use OnionShare to securely share files over the Tor network when needed.
The question of whether to use a VPN alongside Tor Browser is debated among security researchers. A VPN before Tor hides the fact that you are connecting to the Tor network from your ISP, which can be useful in countries that block or monitor Tor usage. However, a VPN shifts trust from your ISP to the VPN provider, and most VPN services keep logs or can be compelled to provide data to authorities. The Tor Project itself does not recommend using a VPN with Tor for most users, since Tor alone provides sufficient anonymity when used correctly. If your ISP blocks Tor, consider using Tor bridges instead, which are unlisted relay nodes designed to circumvent censorship without requiring a third-party VPN provider.
Torzon Access FAQ
Answers to the most common questions about accessing the Torzon marketplace, setting up security features, and using cryptocurrency for anonymous transactions on the platform.
To access Torzon Market safely, download Tor Browser from torproject.org and set the security level to Safest. Get the verified Torzon .onion address from an official source like this page or links.torzondnm.world. Verify the onion URL with the official PGP key before pasting it into Tor Browser. After the login page loads, check your anti-phishing indicators (personal phrase, security image, color scheme) before entering credentials. For maximum security, access Torzon from Tails OS or Whonix rather than your daily operating system.
The official Torzon Market onion address is published on verified sources including access.torzondnm.world, the main clearnet page at torzondnm.world, and the links page at links.torzondnm.world. Always verify any .onion address with the official Torzon PGP key before using it. The marketplace maintains multiple mirror addresses that all connect to the same backend infrastructure. Never trust Torzon links from Telegram groups, social media posts, or unverified forum threads.
A VPN is not required to access Torzon Market through Tor Browser. Tor alone provides sufficient anonymity by encrypting and routing your traffic through three relay nodes. A VPN before Tor hides your Tor usage from your ISP but shifts trust to the VPN provider. If your ISP blocks Tor connections, use Tor bridges instead of a VPN. The Tor Project does not recommend VPN-over-Tor for most users. The most important security measures are using Tor Browser with the Safest setting and verifying onion links with PGP.
Torzon Market accepts both Bitcoin (BTC) and Monero (XMR). The marketplace recommends Monero because its ring signatures, stealth addresses, and RingCT make transactions mathematically untraceable. Bitcoin transactions are recorded on a public blockchain and can be analyzed by chain analysis firms. All payments on Torzon go through a 2-of-3 multisig escrow system regardless of which cryptocurrency you choose. Download the Monero wallet from getmonero.org for the best privacy when using Torzon.
During account setup on the Torzon marketplace, you configure three anti-phishing elements: a personal security phrase that only the real Torzon server can display, a security image chosen from a unique library, and a custom color scheme for your login page. Every time you visit the genuine Torzon Market, all three elements appear exactly as configured. Phishing sites cannot replicate these elements because they are stored encrypted and tied to your specific account session. If any element is missing or incorrect, close the page immediately.
PGP two-factor authentication on Torzon encrypts a random challenge with your public key during login. You decrypt it with your private key and submit the answer to prove your identity. This is stronger than password-based authentication because your private key never leaves your device and cannot be phished, brute-forced, or intercepted by keyloggers. Generate a 4096-bit RSA key with GnuPG and add the public key to your Torzon profile. The platform also supports TOTP authenticator apps and FIDO2/WebAuthn hardware security keys as alternatives.
Both Tails and Whonix provide strong security for accessing the Torzon marketplace, but they serve different use cases. Tails is ideal for temporary sessions because it runs from a USB drive, routes all traffic through Tor, and leaves no trace after shutdown. Whonix is better for persistent use because it runs in virtual machines and allows you to keep files and configurations between sessions while maintaining network isolation. For the highest security, use Whonix inside Qubes OS. Choose Tails if you need portability and amnesia, Whonix if you need persistence and isolation.
Torzon's 2-of-3 multisig escrow creates three keys for each transaction: buyer, vendor, and marketplace. Funds require two signatures to move, so no single party can steal money. In a successful transaction, the buyer and vendor sign together to release payment. In a dispute, the marketplace reviews evidence and signs with the winning party. This prevents the marketplace from performing an exit scam since it only holds one of three keys and cannot unilaterally access funds. The system works with both Bitcoin and Monero on the Torzon platform.
Traditional encryption methods like RSA and ECDSA could theoretically be broken by sufficiently powerful quantum computers. Torzon's post-quantum cryptography uses lattice-based algorithms that resist both classical and quantum attacks. This means that encrypted data captured today will remain protected even if quantum computing advances significantly in the future. Torzon is the first darknet marketplace to implement these algorithms, following the standardization work by the National Institute of Standards and Technology. This forward-looking security measure protects all user data and communications on the platform.
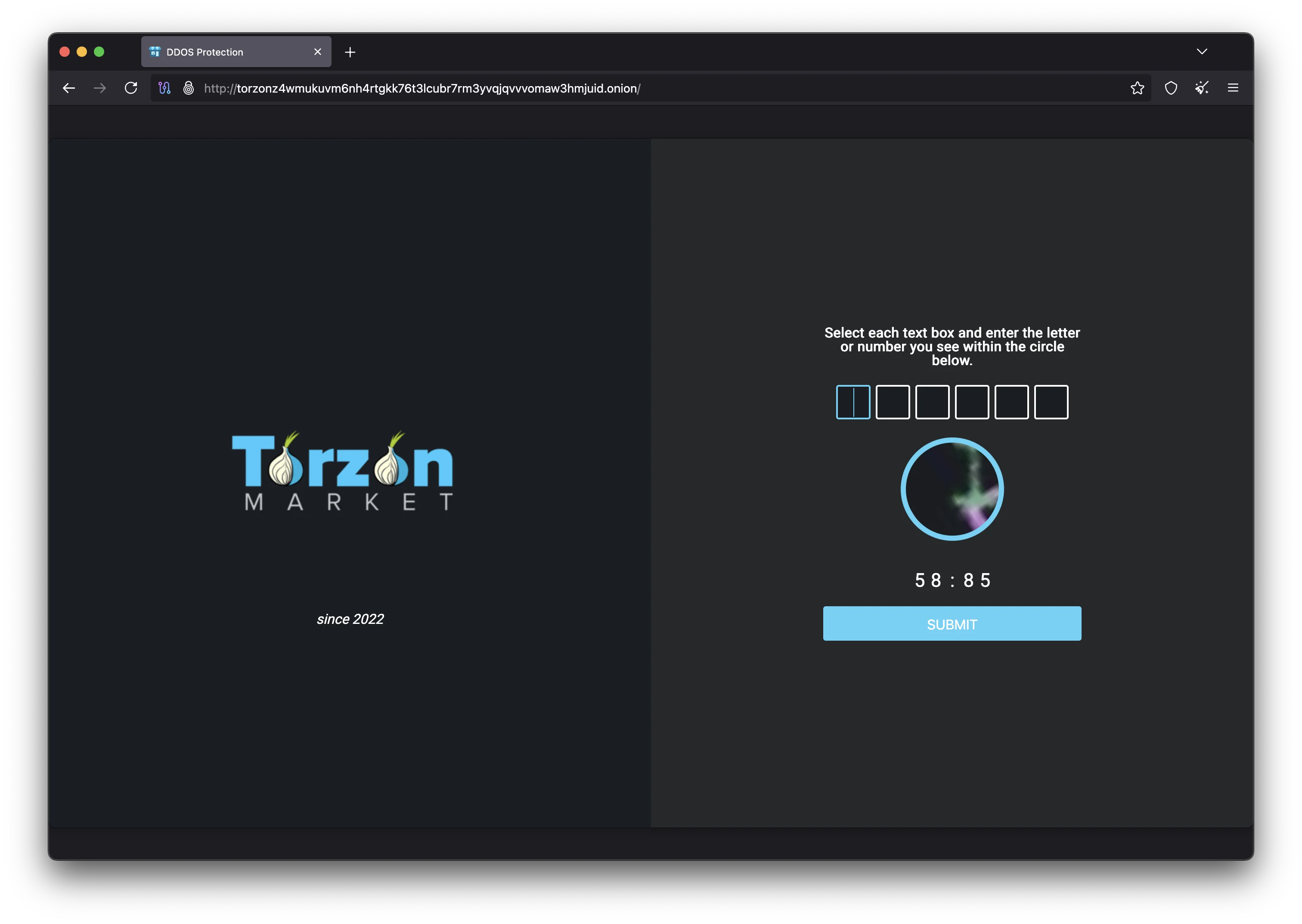
Torzon Market maintains uptime above 98% through distributed infrastructure and DDoS protection systems. The marketplace has operated consistently since its launch in September 2022. If the primary .onion address is temporarily unreachable, users can access the marketplace through verified mirror links published on links.torzondnm.world and other official channels. The Torzon platform uses zero-knowledge RAM-only servers that can be restored quickly after any disruption. Check the official Torzon pages for current mirror status and availability updates.
Ready to Access Torzon Market Safely?
Follow our step-by-step guide to set up Tor Browser, configure PGP authentication, and connect to the Torzon marketplace with verified onion links. Start with the full access guide for detailed instructions on every step of the process.
Last updated: February 18, 2026